Beating Student Proxy Sites Without Playing Whack-a-Mole
Proxy frameworks (Utopia, Lumi, Scramjet, Secured, Arsenic, Ultraviolet, Rammerhead, etc.) don’t win because they’re “new” — they win because they rotate domains faster than you can block them. This is a production pattern that breaks the engine instead of chasing the paint job.
The problem
K-12 environments are getting hammered with proxy sites. Block one, two more appear. URL filtering often struggles because these sites hide inside pages that look legitimate, and categorization is frequently wrong. Domain-based blocking becomes a treadmill.
The shift: stop the engine, not the paint job
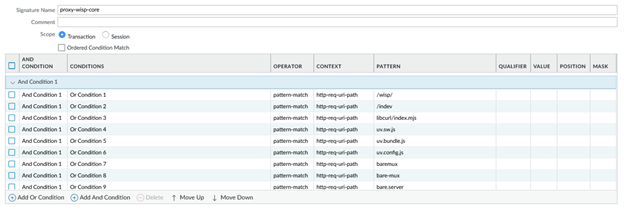
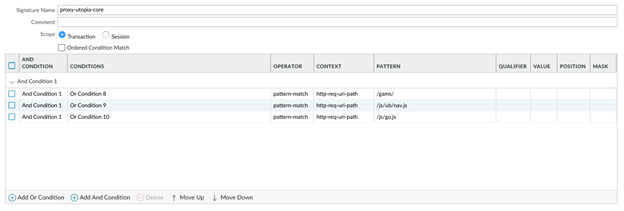
Many of these proxy sites are just different skins built on the same small set of JavaScript frameworks and “skeleton” resources: loaders, bundled assets, workers, handlers, and framework-specific paths that keep showing up across families.
If those core resources can’t load, the proxy can’t initialize — even if the page itself still opens.
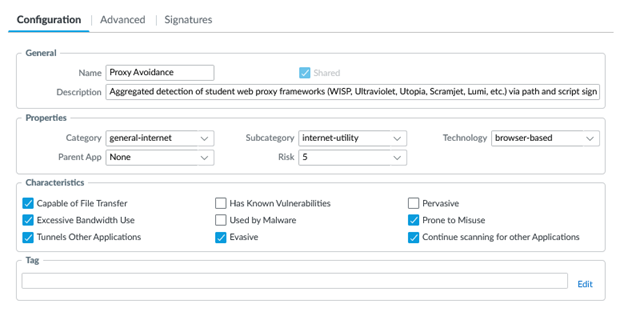
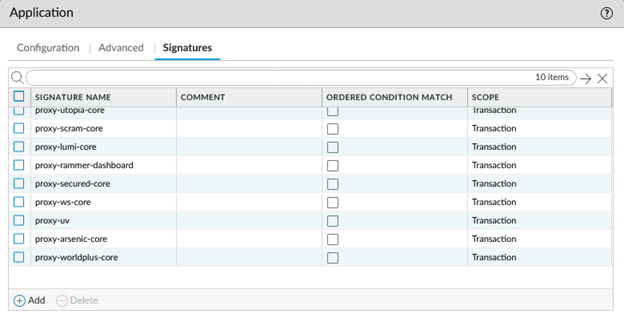
The solution: custom Application + signatures
We built a custom Palo Alto Networks Application and a set of signatures matching those recurring framework resources. It took refinement (and yes, a couple early false positives that we corrected), but the end result has been solid.
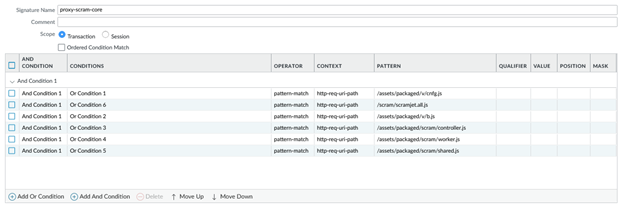
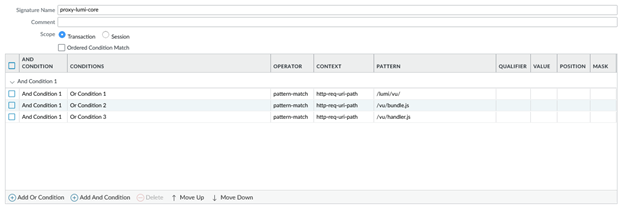
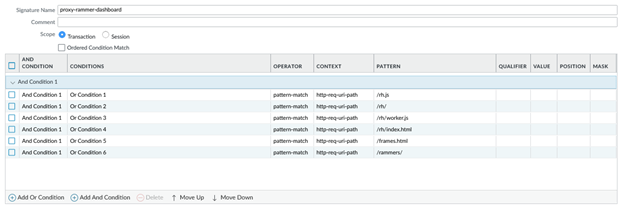
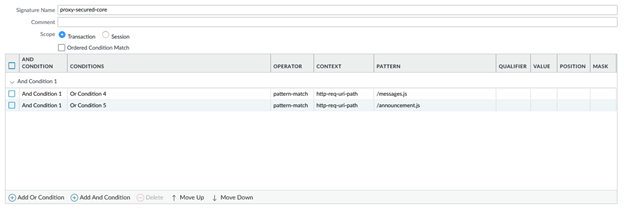
What we match (examples)
Below are examples of signature logic matching recurring framework resources. The value is consistency: domains change constantly, but the scaffolding stays recognizable.


What “success” looks like
This approach doesn’t always produce a traditional block page — because we’re not necessarily blocking the site itself. Instead, the proxy becomes broken because the framework can’t initialize.
You win by identifying and disrupting the shared scaffolding those proxy frameworks depend on.
This post describes an operational pattern (“how to think”). Implementation details should be tested safely in your environment.