Home › Connectivity Beyond the Campus
Secure Internet Access on School Buses
When Chromebooks were issued district-wide, access to learning tools improved immediately. What became clear just as quickly was that learning had moved almost entirely online. For students with long bus rides, connectivity stopped the moment they left campus.
At the same time, Transportation faced a different challenge. Bus camera systems needed to be accessible remotely by administrators without introducing new security risks. Solving these problems independently would have added complexity and operational overhead.
The solution was to treat buses as controlled extensions of the district network rather than isolated endpoints. Cellular connectivity provided transport only. All trust and policy enforcement remained centralized.
Students connected to a guest wireless network on the bus. That traffic was carried over secure tunnels back to district guest firewalls, where the same filtering, logging, and controls used on campus were applied. Transportation video systems followed a separate, isolated path directly to their vendor platform, keeping student and operational traffic cleanly segmented.
This approach avoided special rules and avoided pushing security decisions to the edge. From the student’s perspective, the experience was simple. From the network’s perspective, buses behaved like any other access layer governed by existing policy.
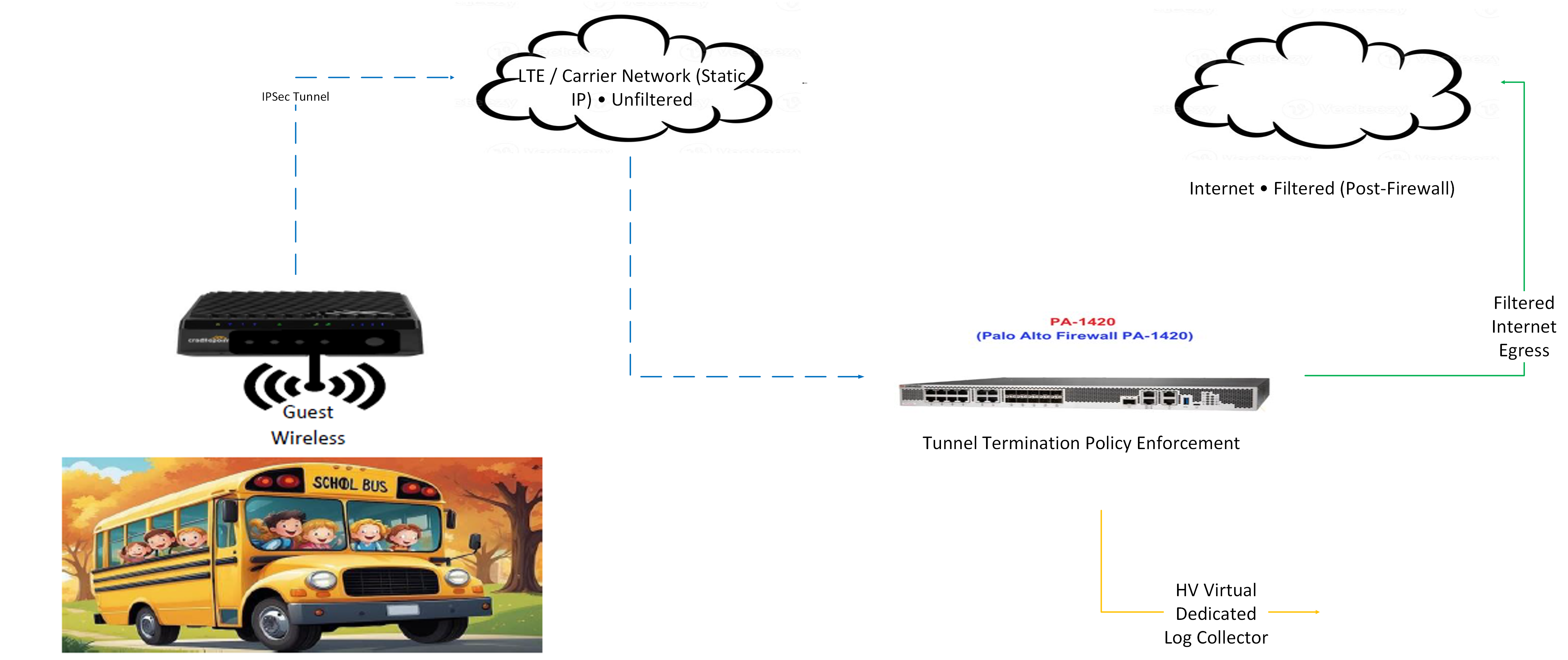
Click the diagram to open the full-size PDF.
What began as a targeted deployment scaled into hundreds of vehicles and established the foundation for everything that followed.